Security of information systems
Today, the information system is a challenging component of data protection because it guarantees the trust of customers and users.
Our methodology
Definition of the scope
Audits

Reporting

Remediation

Awareness-raising

Evaluations
The preliminary and indispensable stage of a security policy
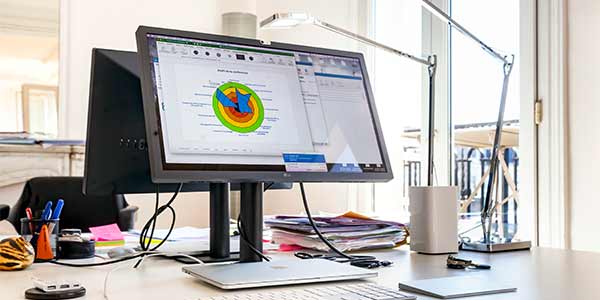
Mappings of the IS
LOB carries out a complete mapping of the network (LAN, WAN, Internet access, redundancy, flow…). This mapping can be completed by an analysis of personal data flows and their control within the framework of the GDPR. It allows us to comprehend the overall configuration of the information system, which is an essential step for any security policy.

External audit
LOB assesses the vulnerability of the IS to an external attacker. The objective is to try to exploit the technical vulnerabilities of the IS in order to:
- Access the internal network and sensitive confidential information (business, emails…)
- Take control of a resource
During these tests, several elements are evaluated such as the robustness of the machines, the security of the services/applications, the perimeter security elements, the security of the authentication systems…
Internal audit
This audit evaluates the level of security of an information system (IS) in several real-life situations.
It involves identifying problems related to the IT infrastructure, the security of workstations, ancillary services deemed to be poorly or inadequately secured, environmental compartmentalization defects, poor configurations, etc…
A fast and close support to our customers to provide serenity and adapted answers
Crisis management
LOB can take action to respond to an emergency following a security incident.
Depending on the nature of the incident, our consultants will be able to:
- Identify as far as possible the source of the intrusion / Forensic
- Conduct a systems inventory
- Measure the extent of the attack and stop it
- Recover the data and ensure the integrity of the IS to ensure rapid restart
- Make preventive and corrective recommendations

Social engineering
The objective is to carry out targeted attacks to stimulate “human failures”. For example by sending malicious emails (phishing, malware attachments) or by using the remote connection tools used by the teams.
This type of audit makes it possible to assess the awareness and responsiveness of the teams to attacks as well as the internal reporting of alerts.
This audit phase is followed by a restitution and awareness-raising to good practices.

Web investigation
- Identify, map sites, blogs, forums/web-based information of particular interest or threat
- Collect as much information as possible on the technical, organisational, legal and financial ecosystem and define indicators or tools to measure their activity
- Monitor these places of exchange, whether commercial or not, in order to detect any changes, modifications to their organisation or proposals
- Make recommendations for action on the basis of the information collected and the observations made
Our operational experience and know-how to raise awareness among your teams
Advice and training
LOB supports its customers during all phases of implementation or improvement of the security of their information systems. In this context we offer:
- An analysis of security needs
- Support in the choice of security products
- A risk analysis, development of security policies and implementation of your business continuity plan
- Training in order to identify and react appropriately to security threats, incidents or alerts and to apply good practices
LOB LINE OF BUSINESS
3 rue Pierre Demours
75017 Paris, France
+33 (0) 1 58 62 10 23